Email Encryption
Goal
IWU Encrypted Email provides message encryption between the sender and recipient, and can be received by any email user, independent of email client or operating system, without installing any software. This will encrypt the entire email including attachments.
Please note:
If you have questions regarding the type of messages or data that should be encrypted, refer to Data Storage and Transmission Policy for assistance.
How to Create an Encrypted Email Message
The following steps illustrate the procedure for creating an encrypted email message originating from within the IWU email system.
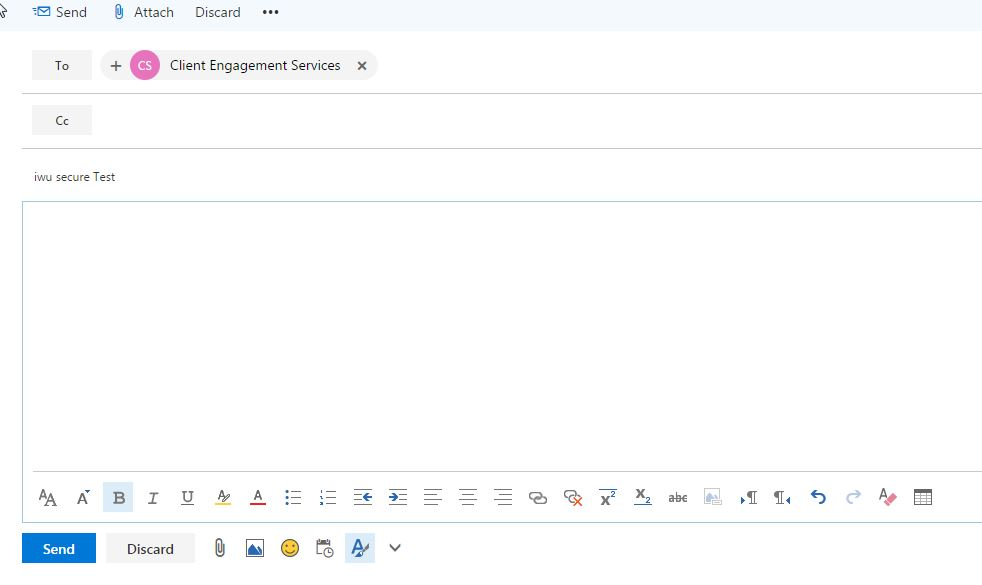
- The sender must include a specific trigger in the subject field of the email for encryption to occur. The subject trigger is: iwu secure. After including the iwu secure trigger, you can follow it with a normal subject line, as seen in Figure 1 below.
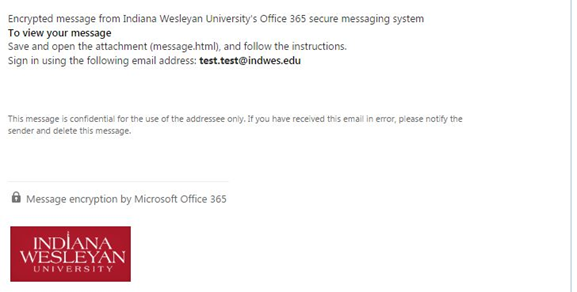
- The recipient will receive a notification that they have received an encrypted message in a few moments. Figure 2 is an example of the message as seen by the recipient.
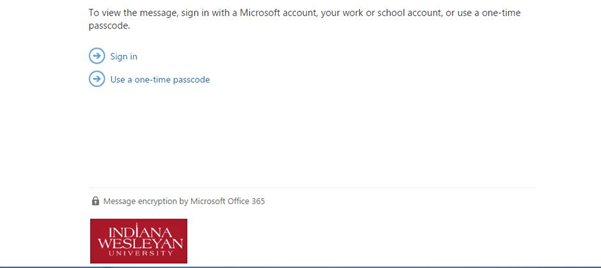
- To open the secure message, the recipient is directed to save and open the attachment. The attachment includes a link to a sign-in page, as seen in Figure 3 below. IWU users can login with their username and password to view the message. External users can either login in with the account the secure email was sent to or click “Use a one-time passcode” in order to sign-in. Because these are secure emails, it is required that you log in each time you access their content.
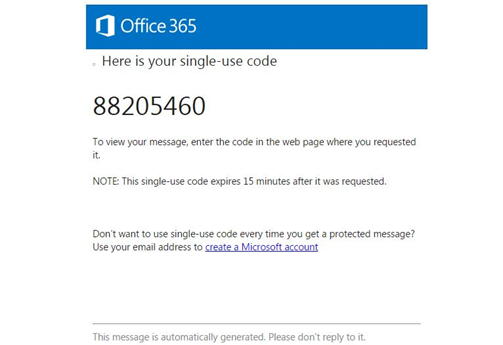
- If the “Use a one-time passcode” in order to sign in is utilized, the one- time use passcode will be delivered to the same email address that the encrypted message was delivered to. They will receive a message like the one in Figure 4 that contains their one-time use passcode.
- Figure 5 shows an example of the contents of an encrypted message, after it has been unlocked for viewing by entering a username and password or a one-time use passcode.

If you have questions regarding the type of data that should be encrypted, refer to Data Usage Parameters for assistance.
*** IWU Secured emails cannot be forwarded to another employee. The only employee with access to the encrypted email is the original recipient/recipients.***
